You trained your staff. They passed the phishing tests. They know not to click suspicious links.
None of that matters anymore.
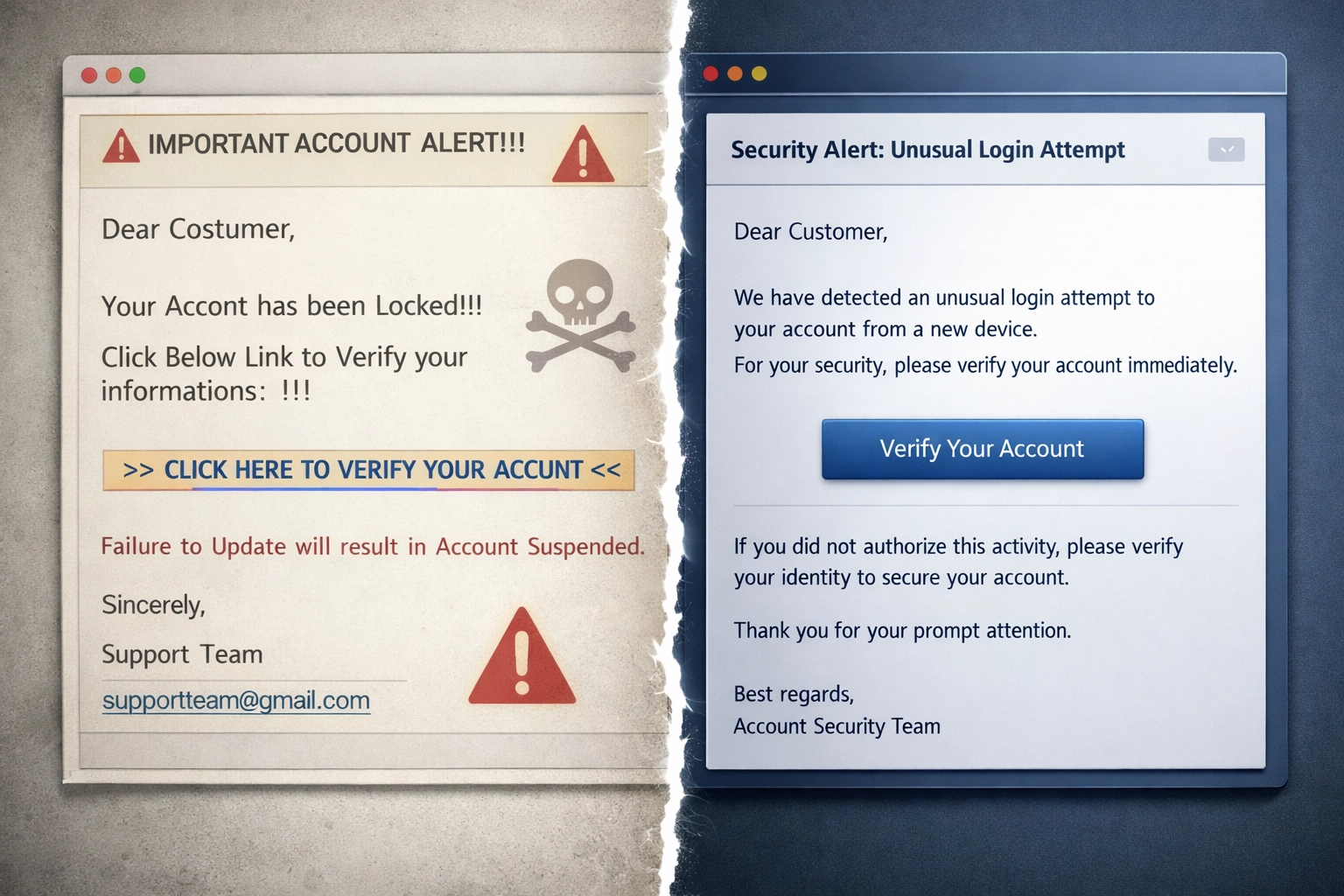
Between September 2024 and February 2025, 82.6 percent of phishing emails contained AI-generated content. The attacks your employees learned to spot: typos, generic greetings, awkward phrasing: are extinct.
The Old Playbook Is Dead
Traditional phishing relied on volume over quality. Attackers sent thousands of identical emails hoping someone would bite. Easy to spot. Easier to block.
That era ended.
AI has removed every telltale sign employees used to identify threats:
Grammatical errors. Gone. AI writes flawless English in any style.
Generic messaging. Eliminated. Every email is personalized using scraped data from LinkedIn, company websites, social media.
Manual limitations. Irrelevant. AI generates thousands of unique variations in seconds.
Security teams now detect one malicious email every 19 seconds. Malware-carrying phishing campaigns rose 204 percent in 2025.

How AI Phishing Works
Conversational hijacking. AI mimics routine exchanges between colleagues. Nearly one-in-five malicious emails now take the form of Business Email Compromise: messages that look like normal internal communication.
Subject line: "Quick question about the invoice"
From: A legitimate-looking executive email
Content: Natural tone. Proper context. Urgency without obvious pressure.
Your employee has no reason to suspect anything.
Polymorphic attacks. AI creates unique versions of the same attack. A Cofense study found 76 percent of initial infection URLs were unique. Eighty-two percent of malicious attachments carried unique hashes.
Traditional filters look for patterns. AI eliminates patterns while scaling attacks.
Behavioral analysis. AI studies employee response times, approval patterns, communication styles. It knows when your team is most likely to respond. What requests they typically approve. How your executives actually write.
Then it replicates all of it.
Why Training Fails Now
Your employees aren't getting worse at security. The threats are getting better at deception.
Speed exceeds human capability. Attackers generate and deploy phishing campaigns faster than any training program can adapt. By the time you update your examples, the attack vectors have evolved.
AI learns from your defenses. When employees report phishing attempts, AI systems analyze what triggered suspicion. Next iteration removes those elements.
No visible indicators remain. The red flags in training materials: misspellings, suspicious sender domains, urgent demands: no longer exist in sophisticated attacks.
Traditional email filters and awareness training depend on detecting known indicators. AI has eliminated those indicators while preserving attack scale.
The Real-World Impact
Small businesses face disproportionate risk. You don't have dedicated security teams monitoring threats 24/7. You rely on employees being vigilant.
That reliance is now a vulnerability.
Invoice fraud. AI-generated emails requesting payment changes look identical to legitimate vendor communications. Employees process hundreds of invoices. One mistake costs thousands.
Credential harvesting. Fake Microsoft 365 login pages are indistinguishable from real ones. AI crafts urgent scenarios that bypass skepticism. One compromised account exposes your entire network.
Data exfiltration. Conversational phishing tricks employees into sharing sensitive files. The request looks routine. The sender appears legitimate. The damage is permanent.
Insurance claims for phishing-related breaches have increased 68 percent since AI tools became widely available. Average cost per incident: $4.88 million for businesses under 500 employees.
What Actually Works
Employee training remains necessary. It's no longer sufficient.
Behavioral detection over content filtering. Network Detection and Response (NDR) and Identity Threat Detection and Response (ITDR) catch anomalous patterns that content-based filters miss.
When a user account suddenly accesses files it never touched before: behavioral detection flags it. When network traffic flows to unusual destinations: NDR catches it. When authentication patterns change: ITDR responds.
AI can fake email content. It cannot fake normal network behavior without creating detectable anomalies.
Multi-factor authentication everywhere. Even if credentials are compromised, MFA prevents unauthorized access. No exceptions. No "I'll set it up later." Enforce it now.
Email authentication protocols. DMARC, DKIM, and SPF validation prevent domain spoofing. Configure them correctly. Monitor them continuously.
Controlled automation. Combine automated detection with human validation. AI tools can analyze email patterns faster than humans. Humans provide context AI lacks. Both are required.

What Managed IT Security Provides
In-house staff handle daily operations. They don't have time to monitor evolving threat landscapes, update security configurations, or respond to alerts 24/7.
Managed security fills that gap:
Continuous monitoring. Security operations centers watch for anomalous behavior around the clock. They catch threats during off-hours when your team isn't watching.
Threat intelligence. Managed providers aggregate attack data across multiple clients. They identify emerging patterns before they reach your network.
Rapid response. When behavioral detection flags an issue, response teams investigate immediately. Not "when someone has time." Immediately.
Security stack management. EDR, email security, network monitoring, backup verification: managed services maintain and optimize the entire security infrastructure. Your team focuses on business operations.
Regular security assessments. Quarterly reviews identify gaps before attackers do. Configurations drift. Employees bypass controls. Regular audits catch these issues.
Shifting Your Security Model
Stop asking "Can my employees spot this phishing email?"
Start asking "What happens when a phishing email succeeds despite our best efforts?"
Assume breach mentality. Design security controls expecting that some attacks will succeed. Limit lateral movement. Segment critical systems. Maintain offline backups.
Zero trust architecture. Verify every access request regardless of source. User inside your network requesting a file? Verify. Application accessing data? Verify. No implicit trust.
Incident response planning. Document procedures before incidents occur. Who gets notified? What systems get isolated? Where are backups stored? How do operations continue?
Organizations that implement these approaches reduce successful phishing impacts by 91 percent even when initial attacks bypass email filters.

The Timeline for Action
AI-powered phishing isn't a future threat. It's current reality.
Attackers are already using these tools. Your competitors are already implementing behavioral defenses. Insurance carriers are already raising premiums for businesses without adequate controls.
This quarter: Audit current email security. Verify MFA is enforced everywhere. Review user access permissions.
Next quarter: Implement behavioral detection tools. Establish baseline network patterns. Configure automated alerting.
Ongoing: Partner with managed security providers for 24/7 monitoring and response capability.
Employee training continues. Add it to the foundation, not the entire structure.
Moving Forward
Your employees remain your first line of defense. They can't be your only line of defense.
AI has fundamentally changed the threat equation. Sophisticated attacks now scale infinitely while appearing completely unique. Pattern-based defenses fail. Static training fails. Perimeter security fails.
Behavioral detection, continuous monitoring, and rapid response capability succeed.
Small businesses face enterprise-level threats without enterprise-level resources. Managed security services level that playing field.
The question isn't whether AI-powered phishing will target your business. The question is whether you'll have the controls in place when it does.
We provide managed IT security solutions designed specifically for small and mid-sized businesses. Behavioral detection, 24/7 monitoring, and rapid incident response: without requiring dedicated in-house security staff.
Contact us to schedule a security assessment. We'll identify current vulnerabilities and provide actionable recommendations for your specific environment.
Your employees are trained. Now make sure they're protected.

